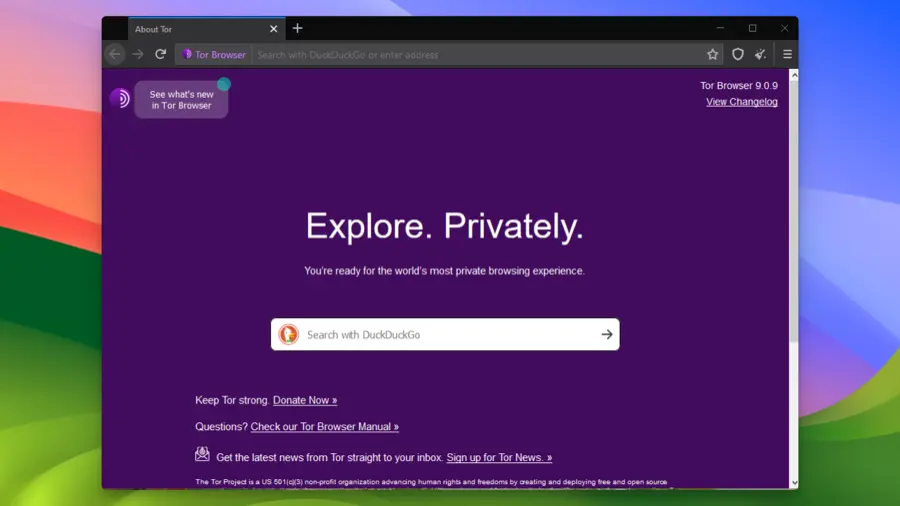
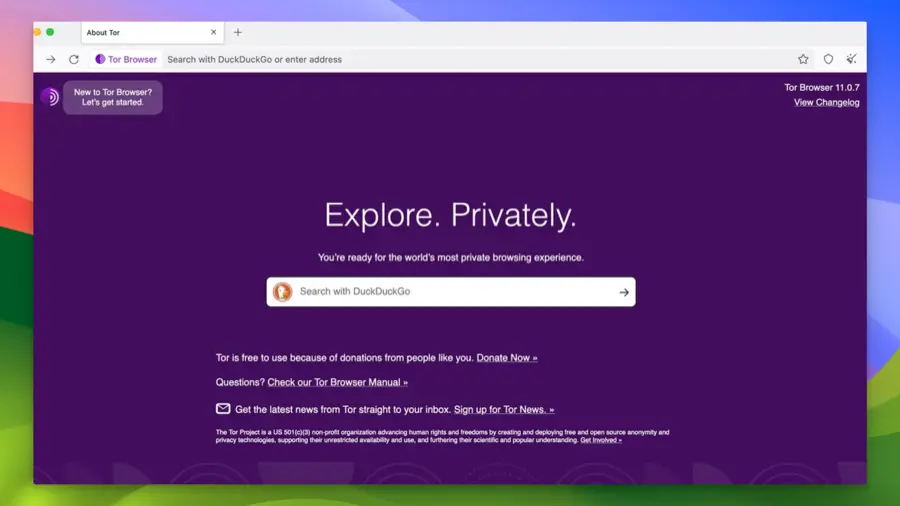
"Navigate the Net Anonymously with Tor.”
Tor Browser is a free and open-source web browser that prioritizes privacy and anonymity. Utilizing the Tor Network, it encrypts and routes internet traffic through multiple layers, masking users’ IP addresses and protecting their online identity. It’s a popular choice for accessing the dark web and maintaining online privacy.
Main Features
Multi-Layered Encryption
Tor Browser provides multi-layered encryption, ensuring secure browsing. It routes traffic through multiple nodes, encrypting data at each step, making it difficult for anyone to trace the user’s online activities.
Access to the Dark Web
With Tor Browser, users can access the dark web, a hidden part of the internet where anonymity is preserved. It’s a space often associated with privacy-focused communication and anonymous transactions.
Automatic Data Erasure
Tor Browser automatically erases browsing history, cookies, and cached data after each session. This automatic data erasure feature ensures that no personal information is stored or left behind.
Geo-Restricted Content Access
Tor Browser allows users to view geo-restricted content by masking their actual location. This feature enables access to content that might be blocked in certain regions or countries.
Built-in Privacy Features
Tor Browser comes with built-in privacy features like tracker blockers and fingerprinting protection. These features provide an additional layer of security, making browsing safe and private.
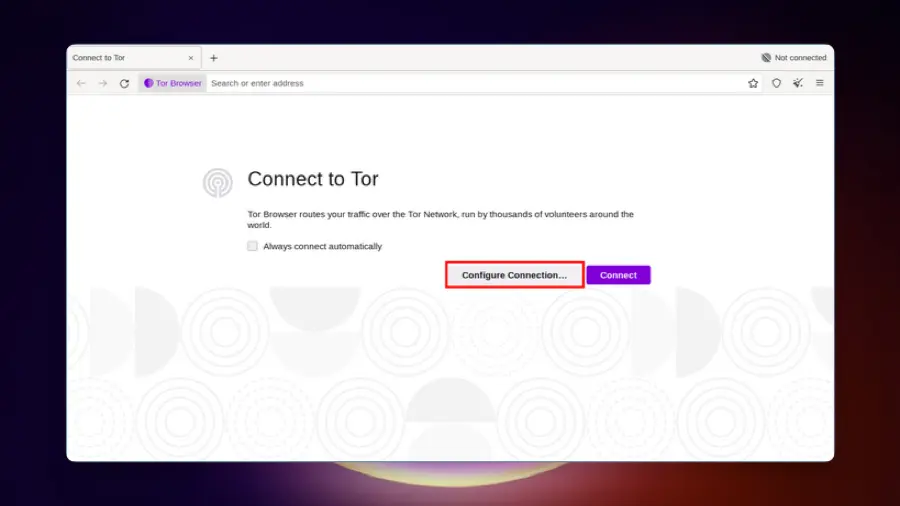
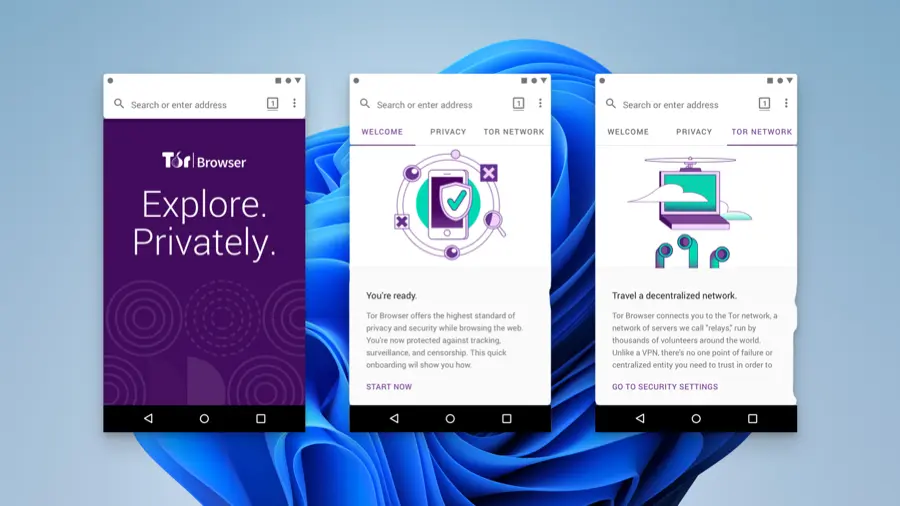
Easy Installation Process
The easy installation process of Tor Browser makes it accessible to all users. Whether it’s Tor Browser for PC, Tor Browser Mac, or Tor Browser Android, the installation is straightforward.
Legal and Ethical Use
While Tor Browser is legal and endorsed by privacy advocates worldwide, it’s essential to use it responsibly. Legal and ethical use ensures that the browser’s powerful features are used for legitimate purposes.
Review
The Tor Browser stands as a paramount tool for users worldwide seeking anonymity and security while navigating the internet. This review delves into the components, usability, and the extensive privacy features offered by the Tor Browser, providing a comprehensive look at its capabilities.
A Deep Dive into Anonymity
The Tor Browser is renowned for its ability to provide anonymous access to the internet. It is a product of the Tor project, a non-profit organization with a focus on developing privacy-centric technologies. The browser is open-source, allowing for transparency and trustworthiness, and is a proven solution for those wanting to browse the internet without leaving a trace. It is especially beneficial for journalists, political activists, and users in regions with stringent internet censorship, enabling them to report and access information freely and securely.
How Does Tor Work?
The browser operates by routing user data through a network of volunteer-operated servers, or nodes, encrypting the traffic multiple times. This multi-layered encryption ensures that the user’s location and browsing data remain secure and untraceable. The connection travels through an entry node, relay node, and finally, an exit node, each step reinforcing the user’s anonymity. This extensive routing and encryption make the Tor Browser one of the most secure options available for accessing both the surface and the dark web.
User Experience & Accessibility
Tor offers a straightforward and understandable user interface, making it easy for users to navigate the web securely. The installation process is uncomplicated, with guides available for different operating systems, allowing users to set up and start browsing in minutes. The browser automatically erases browsing history and cookies, defending against surveillance and ensuring user privacy.
Accessing the Unaccessible
One of the standout features of the Tor Browser is its ability to bypass geo-restrictions and network bans, granting users access to otherwise blocked content and websites. This feature is particularly useful for accessing information that is restricted in certain regions or censored by local authorities. The browser also allows users to explore onion websites, which are specific to the dark web, expanding the scope of accessible content.
Speed & Performance
While the Tor Browser is a powerful tool for privacy, the extensive routing can lead to slower browsing speeds compared to conventional browsers. However, the level of security and anonymity it provides outweighs the minor inconvenience of reduced speed for users prioritizing privacy.
Legal & Ethical Considerations
Using the Tor Browser is legal in most jurisdictions, but it is crucial to use it responsibly. Some individuals may use it for illicit activities, but the primary purpose of Tor is to offer a secure and anonymous browsing environment. It is a trustworthy and scientific tool developed to advance human rights and freedoms by protecting users from tracking, surveillance, and censorship.
Conclusion
The Tor Browser emerges as a beacon of hope in the realm of online privacy. It is a robust and reliable solution for those seeking to protect their anonymity and security on the internet. The browser’s ability to access blocked content and its steadfast focus on user privacy make it an invaluable asset for internet users worldwide. While the browsing speed may be a minor drawback, the extensive privacy features and the secure browsing environment offered by Tor make it a preferred choice for those valuing online security and freedom.
Who should use
Tor Browser is recommended for journalists, activists, privacy enthusiasts, and anyone looking to protect their online identity. Its unique features cater to those who prioritize security and anonymity in their online activities.
Pros
- Strong Privacy
- Dark Web Access
- Free to Use
Cons
- Slower Speed
- Complex for Newbies
- Potential Misuse
Alternative App
1. Brave Browser
- Features: Built-in ad blocker, tracker blocker, and Tor integration for private browsing.
- Pros: Fast, user-friendly, and offers a high level of customization.
- Cons: Some users may prefer more open-source options.
2. Firefox Focus
- Features: Blocks a wide range of online trackers, erases your browsing history, and minimalistic design.
- Pros: Lightweight and user-friendly.
- Cons: Limited features compared to full-fledged browsers.
3. DuckDuckGo Privacy Browser
- Features: Forces sites to use an encrypted connection, blocks trackers, and provides a privacy grade for each website.
- Pros: Emphasizes user privacy and doesn’t track searches.
- Cons: Limited customization options.
4. I2P (Invisible Internet Project)
- Features: End-to-end encryption, decentralized, and supports anonymous browsing, chatting, and file sharing.
- Pros: Strong privacy protection.
- Cons: Steeper learning curve and slower than regular browsing.
5. Waterfox
- Features: Open-source, focused on speed and ethical user choices.
- Pros: Customizable and respects user privacy.
- Cons: May not be as secure as some other options.
6. Safari (with Privacy Mode)
- Features: Intelligent Tracking Prevention, sandboxing, and built-in password manager.
- Pros: Fast, energy-efficient, and integrated into the Apple ecosystem.
- Cons: Available primarily on Apple devices.